Set up OKTA SSO with Hippo
Introduction
This tech note discusses how to set up OKTA Single Sign On (SSO) with Hippo V6.
What is Single Sign On (SSO)
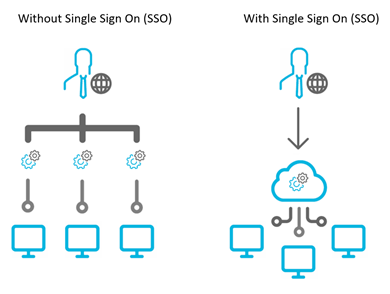
Single Sign On (SSO) is a new feature utilized by Hippo that simplifies the login procedure.
Single Sign On (SSO) is an authentication process that allows the user to access multiple applications with a single set of login credentials (username and password). One of these applications can be Hippo CMMS.
How does it work?
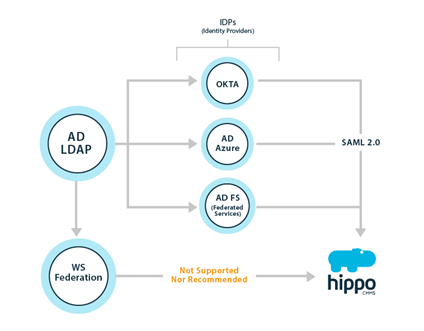
In Hippo, SSO is managed by an identity provider. The role of an identity provider is to allow for reliable integration for SSO to all your applications, including Hippo. Examples of identity providers include Active Directory Federated Services (AD FS), Active Directory Azure, and Okta.
Hippo CMMS v6 will support Okta identity provider by default. To read more about Okta, please visit: https://www.okta.com/products/single-sign-on/
I have Okta as an Identity Provider. How do I set it up to work with Hippo?
The first step in configuring Hippo to support SAML based Single Sign-On from Okta is to set up Hippo in Okta.
In SAML terminology, what you will be doing here is configuring Okta (your SAML Identity Provider or “SAML IdP”), with the details of Hippo (the new SAML Service Provider or “SAML SP”).
Here is how to set up a Hippo in Okta:
If you are using the developer dashboard you will first need to switch to the Classic UI. If you see a < > Developer prompt in the top left, click it and select Classic UI to switch to the Classic UI.
Log in to your Okta organization as a user with administrative privileges. If you don’t have an Okta organization, you can create a free Okta Developer Edition organization.
Click on the blue “Admin” button

Click on the “Add Applications” shortcut

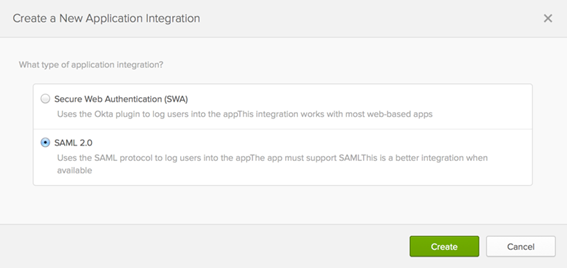
Click on the green “Create New App” button

In the dialog that opens, select the “SAML 2.0” option, then click the green “Create” button
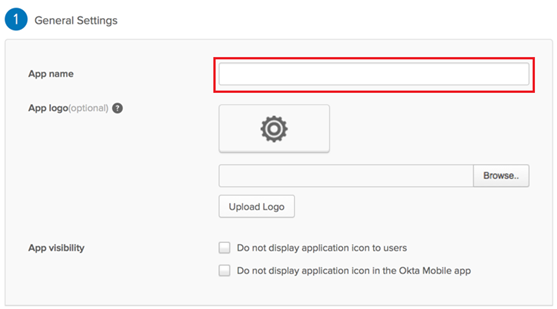
In Step 1 “General Settings”, enter “Hippo” in the “App name” field. In the image below, the field is highlighted in red. (Optional: You can add an image. In the attachments section at the bottom of this technote, you can download the Hippo logo.) Then, click the green “Next” button.
In Step 2 “Configure SAML,” section A “SAML Settings”, enter
or
https://auth.hippocmms.ca (If your login URL ends with .CA)
below into the “Audience URI (SP Entity ID)” field (Note that there's no trailing slash at the end of the URL). Next, enter https://auth.hippocmms.com/sso/provi...nt_id=clientID
or
https://auth.hippocmms.ca/sso/provid...nt_id=clientID
replacing clientID with your company Client ID, into the “Single sign on URL” field (Note that there's no trailing slash at the end of the URL).
These fields are highlighted in red also:
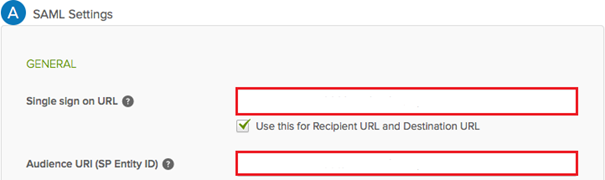
In the “Attribute Statements” section, add three attribute statements:
“FirstName” set to “user.firstName”
“LastName” set to “user.lastName”
“Email” set to “user.email”
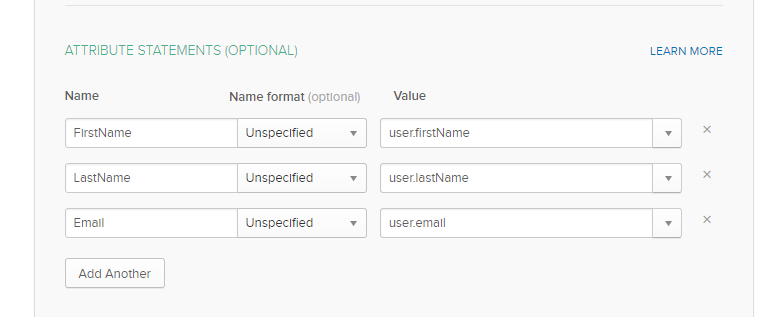
Click Next to continue.
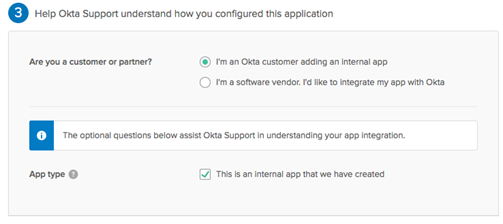
In Step 3 “Feedback”, select “I’m an Okta customer adding an internal app”, and “This is an internal app that we have created,” then click Finish.
The “Sign On” section of Hippo appears. Keep this page open it a separate tab or browser window. You will return to this page later in this guide and copy the “Identity Provider metadata” link. (To copy that link, right-click on the “Identity Provider metadata” link and select “Copy”)
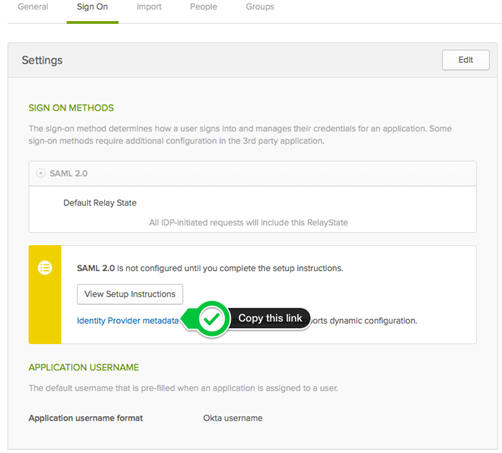
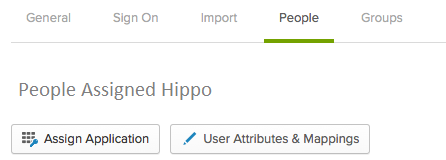
Next, click on assignments. Right-click on the “People” section of Hippo and select “Open Link In New Tab” (so that you can come back to the “Sign On” section later).
In the new tab that opens, click on the “Assign Application” button
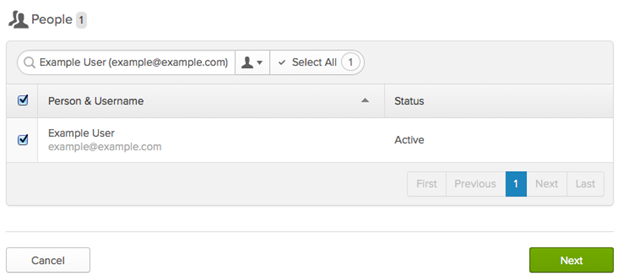
A dialog titled “Assign Hippo to up to 500 people” will open. Type your username into the search box, select the checkbox next to your username, then click the green “Next” button
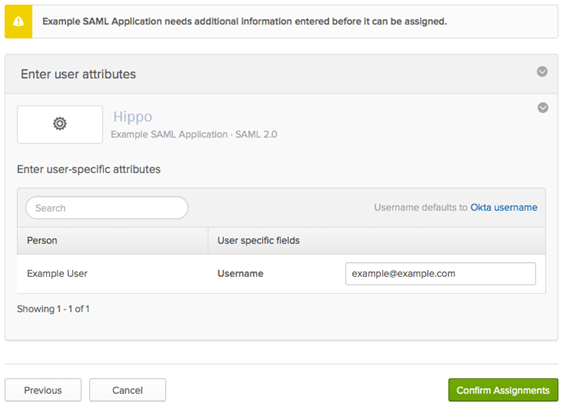
You will be prompted to “Enter user-specific attributes”. Just click the green “Confirm Assignments” button to keep the defaults.
You are now ready to configure SAML Hippo. The information in the tab you opened in step #10 contains the information that you’ll need to configure SAML in Hippo. It is recommended to copy the metadata file into notepad and save as a .txt file. Please send this information to support@hippocmms.com along with your clientID.
